2022-04-22 Emotet Malspam Using Excel 4 Macro

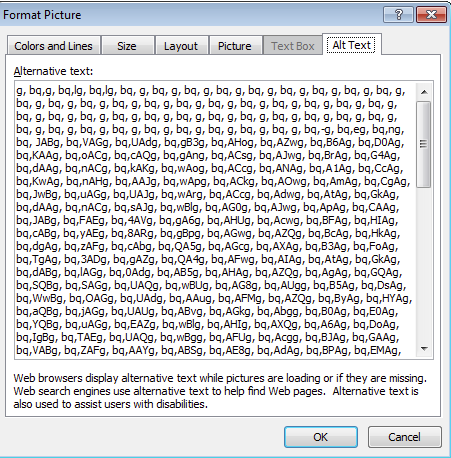
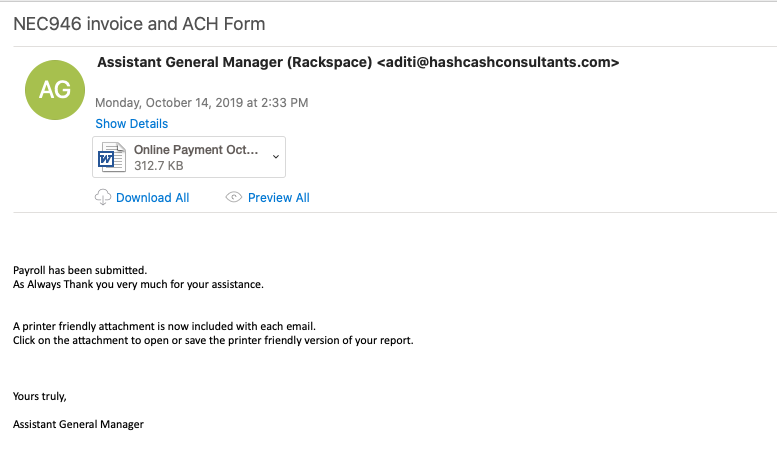
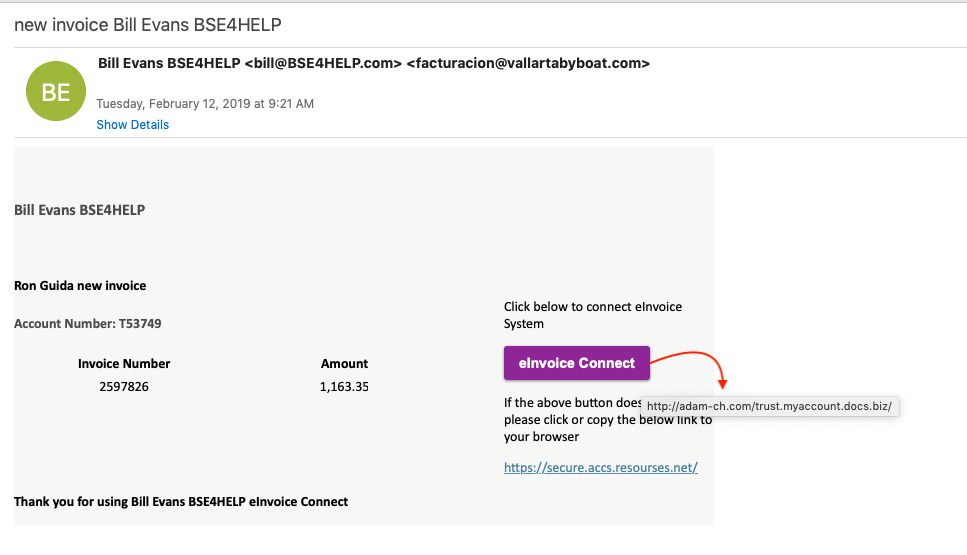
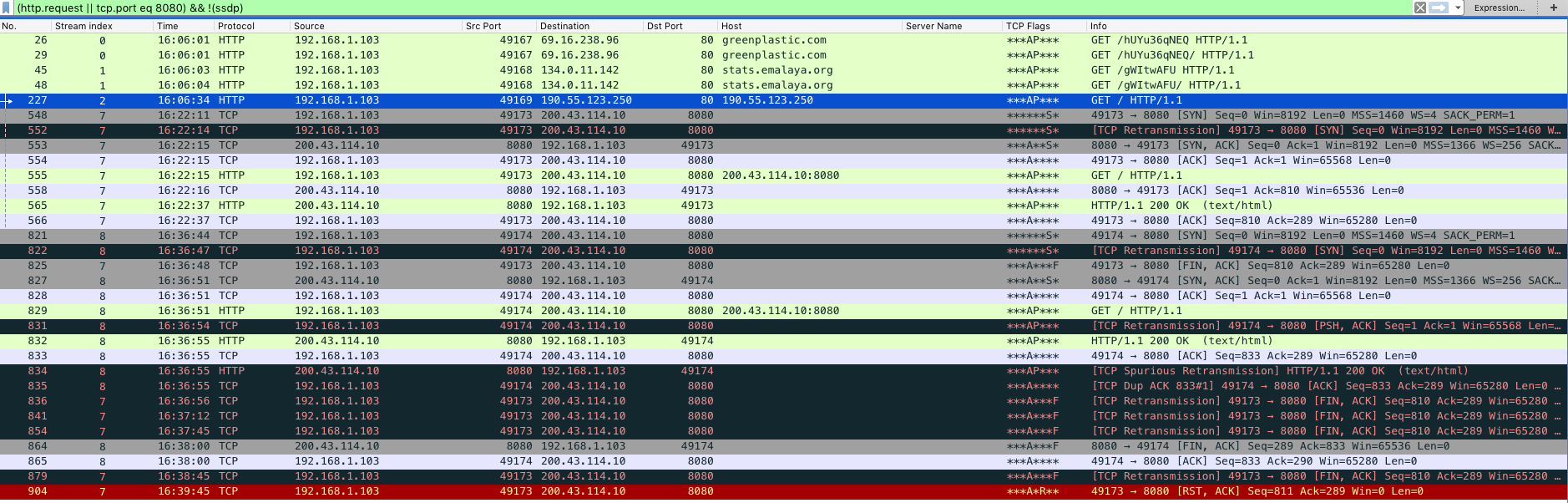
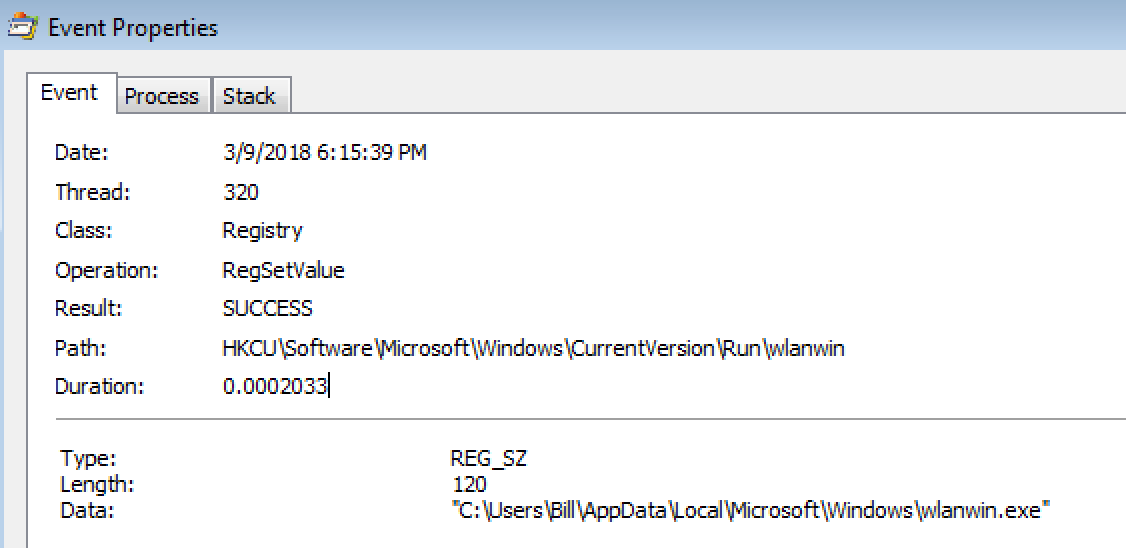
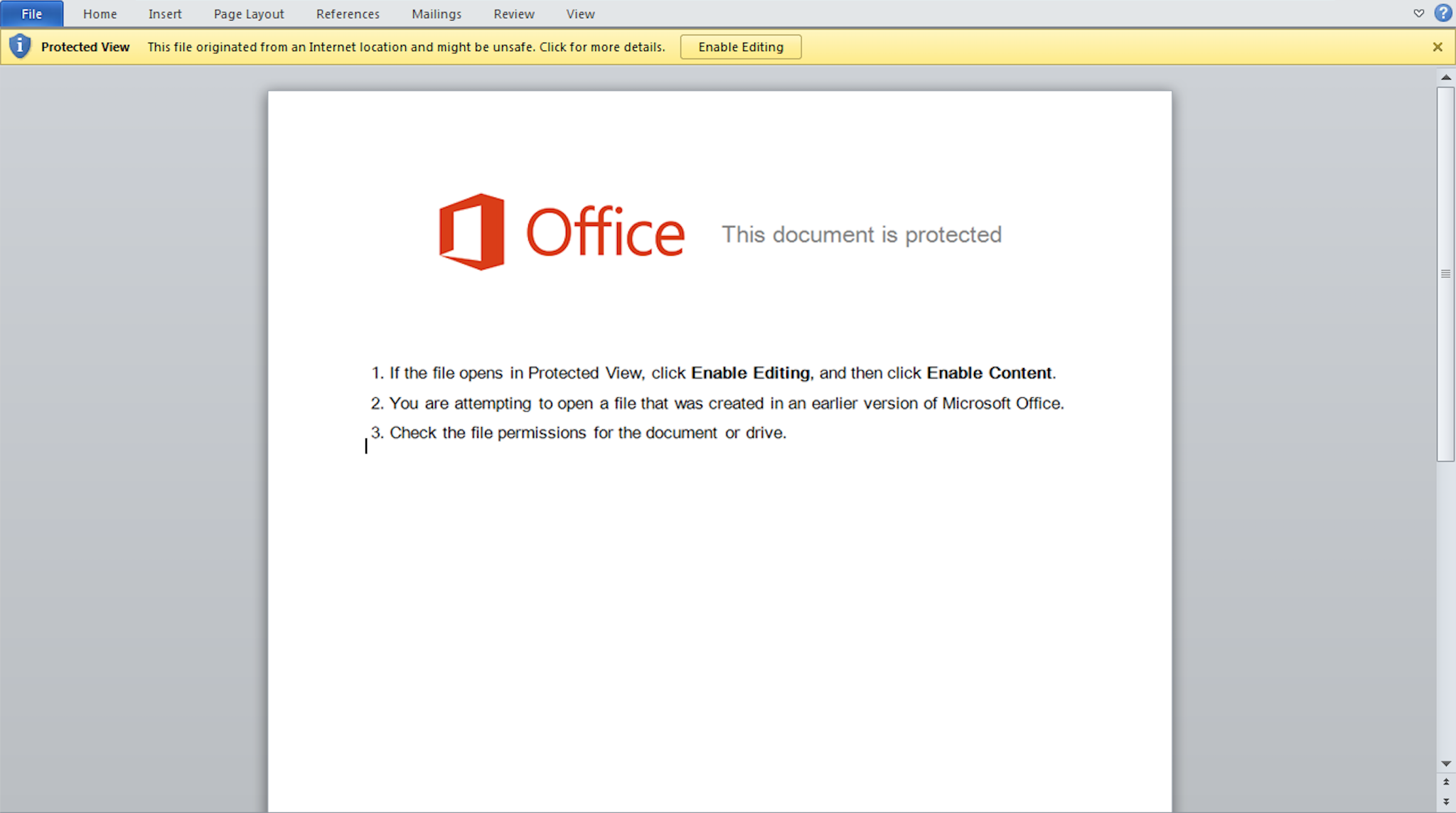
Summary ======== Looking at the mail filters yesterday to see if there was anything interesting while having “some” downtime during the late part of my shift, I was able to come across a sample of some Emotet malspam leveraging the usual hacked/injected email thread. The sample was an encrypted zip file that had an Excel spreadsheet using the Excel 4 macro once the macro was enabled. All the files and artifacts from this can be found over at my Github repo located here. Analysis ======== Host ———- This infection chain is very much like the one that I detailed in…